Cloud & AI Security
Cloud app security, AI governance, Microsoft Defender for Cloud Apps, and lifecycle workflows.
AI governance and cloud app security — deployed, not just discussed.
Cloud services and AI agents are expanding the attack surface faster than traditional security models can adapt. From shadow AI tools exfiltrating classified data to unmanaged service principals with excessive permissions, nine insider and network risks demand new governance frameworks. Defender for Cloud Apps, Global Secure Access, and AI agent governance provide the visibility and control needed to embrace innovation without compromising security posture.
Added in Endpoint (Plan 2)
- Global Secure Access - M365 — Microsoft Entra Global Secure Access for M365 traffic
- Global Secure Access - Internet — Microsoft Entra Global Secure Access for internet traffic, web filtering, and Private Access tunnels
- External Identity & B2B Governance — Guest governance, cross-tenant access policies, external collaboration settings, and partner onboarding processes
- Defender for Cloud & CSPM — Azure Defender for Cloud plans (Servers, Containers, Databases) and Cloud Security Posture Management with Secure Score
Added in Information Governance (Plan 3)
- Lifecycle Workflows — Entra ID Governance lifecycle workflows for pre-hire, joiner, mover, and leaver identity lifecycle automation
- AI Agent Identity & Governance — Entra Agent ID registration, agent lifecycle policies with human sponsor requirement, CA for AI workloads
- AI Data Governance — Sensitivity labels on AI-consumed data, DLP policies for AI-generated content, Copilot governance configuration
- AI Monitoring & Shadow AI Detection — AI agent action audit logging, Copilot usage monitoring, shadow AI detection via Entra Internet Access and Sentinel
- MCP Server Security — MCP server authentication (Device Flow, API keys), least-privilege tool exposure, connectivity monitoring
What you receive
| Delivery Package | Duration | Stakeholders | Key Deliverables |
|---|---|---|---|
| Global Secure Access | 5–15 days | Network Admin, CISO | M365 traffic profile configuration; Web content filtering policies; Private Access per-app configuration; Network segmentation assessment |
| External Identity & B2B Governance | 3–8 days | CISO, IT Admin, Legal | Cross-tenant access policy; Guest lifecycle governance; Partner onboarding checklist; External user inventory and cleanup |
| Identity Governance & Lifecycle | 8–20 days | HR, IT Admin, Line Managers | Role-to-access package mapping; Lifecycle workflow definitions; HR connector configuration; Joiner/mover/leaver automation |
| Defender for Cloud & CSPM | 3–8 days | Cloud Admin, CISO | Defender plan enablement per subscription; Secure Score baseline; Security recommendation triage; Alert forwarding to Sentinel |
| AI Governance & Security | 5–15 days | CISO, AI/ML Engineering, DevOps | AI agent inventory; Agent lifecycle governance policy; AI data classification policy; Shadow AI detection rules; MCP server security baseline |
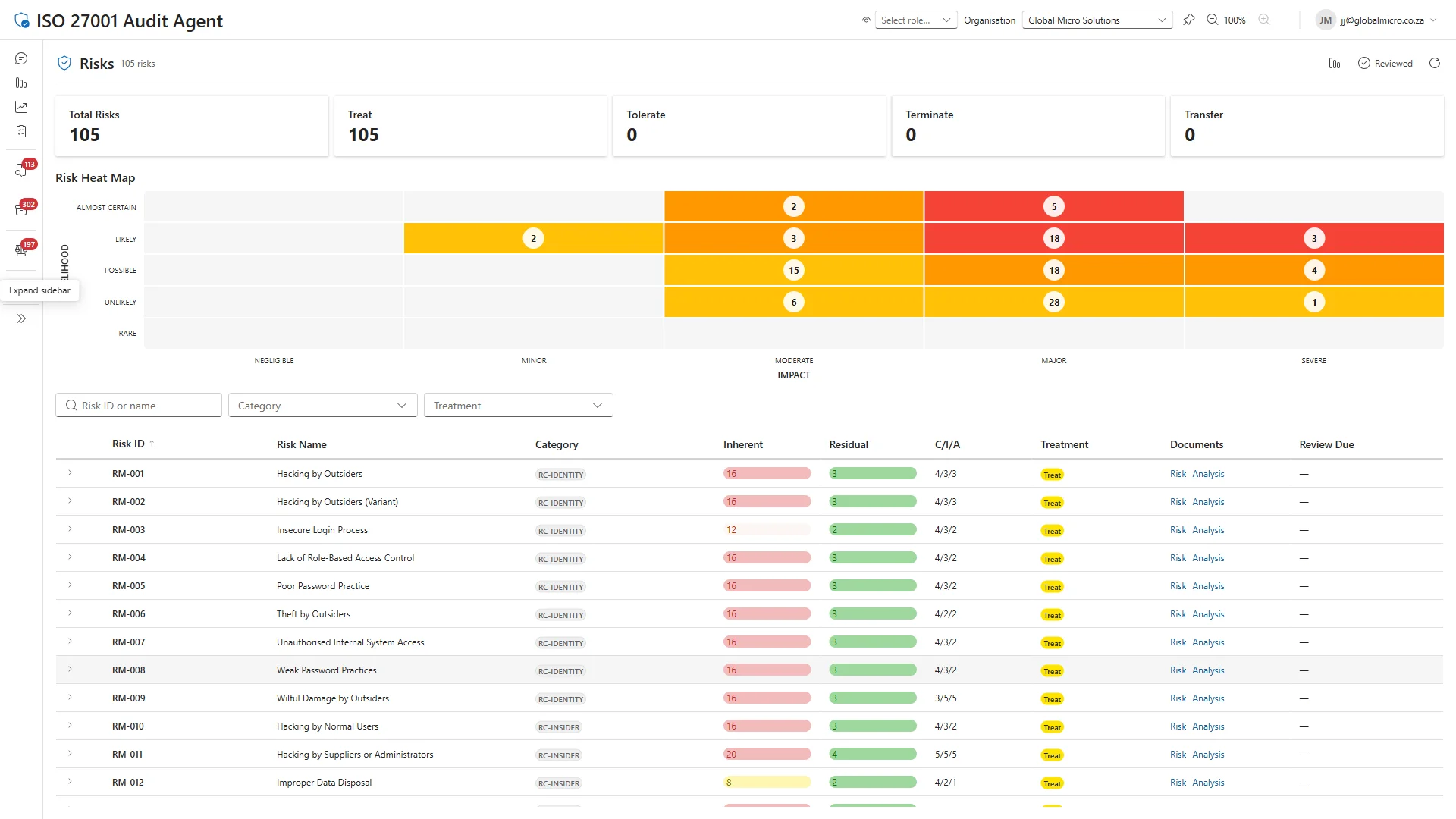
Risk impact
| Risk | Before | After | Reduction |
|---|---|---|---|
| Hacking by Suppliers or Administrators | 20 | 4 | 80% |
| Theft by Insiders | 20 | 4 | 80% |
| Wilful Damage by Insiders | 20 | 4 | 80% |
| Hacking by Normal Users | 16 | 3 | 81% |
| Misuse of Rights and Systems | 16 | 3 | 81% |
Risk scores use a likelihood × impact matrix (1–25). Lower is better.
Ready to see where you stand? Our free assessment benchmarks your cloud & ai security against these capabilities — in 30 minutes, no tenant access required. Start your assessment.
ISO 27001 controls covered
- A.5.12 Classification of Information
- A.5.13 Labelling of Information
- A.5.15 Access Control
- A.5.16 Identity Management
- A.5.19 Information Security in Supplier Relationships
- A.5.20 Addressing Information Security within Supplier Agreements
- A.6.1 Screening
- A.6.5 Responsibilities After Termination or Change of Employment
- A.8.1 User Endpoint Devices
- A.8.15 Logging
- A.8.16 Monitoring Activities
- A.8.20 Networks Security
- A.8.23 Web Filtering
- A.8.25 Secure Development Life Cycle
- A.8.26 Application Security Requirements
- A.8.9 Configuration Management