Security Awareness & Human Risk
Awareness training, phishing simulations, and automated A.6.3 compliance evidence.
Your people trained, tested, and evidenced for ISO 27001 A.6.3.
Most organisations invest in awareness training and hope for the best. They run an annual phishing test, send a compliance email, and file the results in a spreadsheet the auditor will never trust. We take a dual-platform approach: structured education through our branded CyberAware platform, and real-world phishing simulations through Microsoft Defender — delivering an average 80% reduction in human risk within eight months. Then we prove it. The Awareness Register in the Audit Agent tracks every learner, every campaign, every trend — and feeds it directly into your ISO 27001 A.6.3 evidence. Your auditor will verify it. The evidence is already there.
Foundation (Plan 1)
- CyberAware Security Awareness Platform — Branded CyberAware platform with 80+ animated videos dramatising real-world cyber events, 100+ phishing templates updated for current threats, auto-enrolment across all tenants, branded ‘You’ve Been Phished’ contextual training pages, human risk scoring with visual graphs, gamified leaderboards, and exportable branded PDF reports. Average 80% risk reduction from baseline within 8 months.
Added in Endpoint (Plan 2)
- Attack Simulation Training — Phishing simulations delivered directly to user mailboxes via Microsoft Defender for Office 365 Plan 2 — credential harvesting, malware attachments, and QR code lures that mirror real attacker tactics. Automated remedial training triggers on failure. Results integrate with Defender XDR alongside real threat data, giving a unified view of simulated and actual phishing resilience.
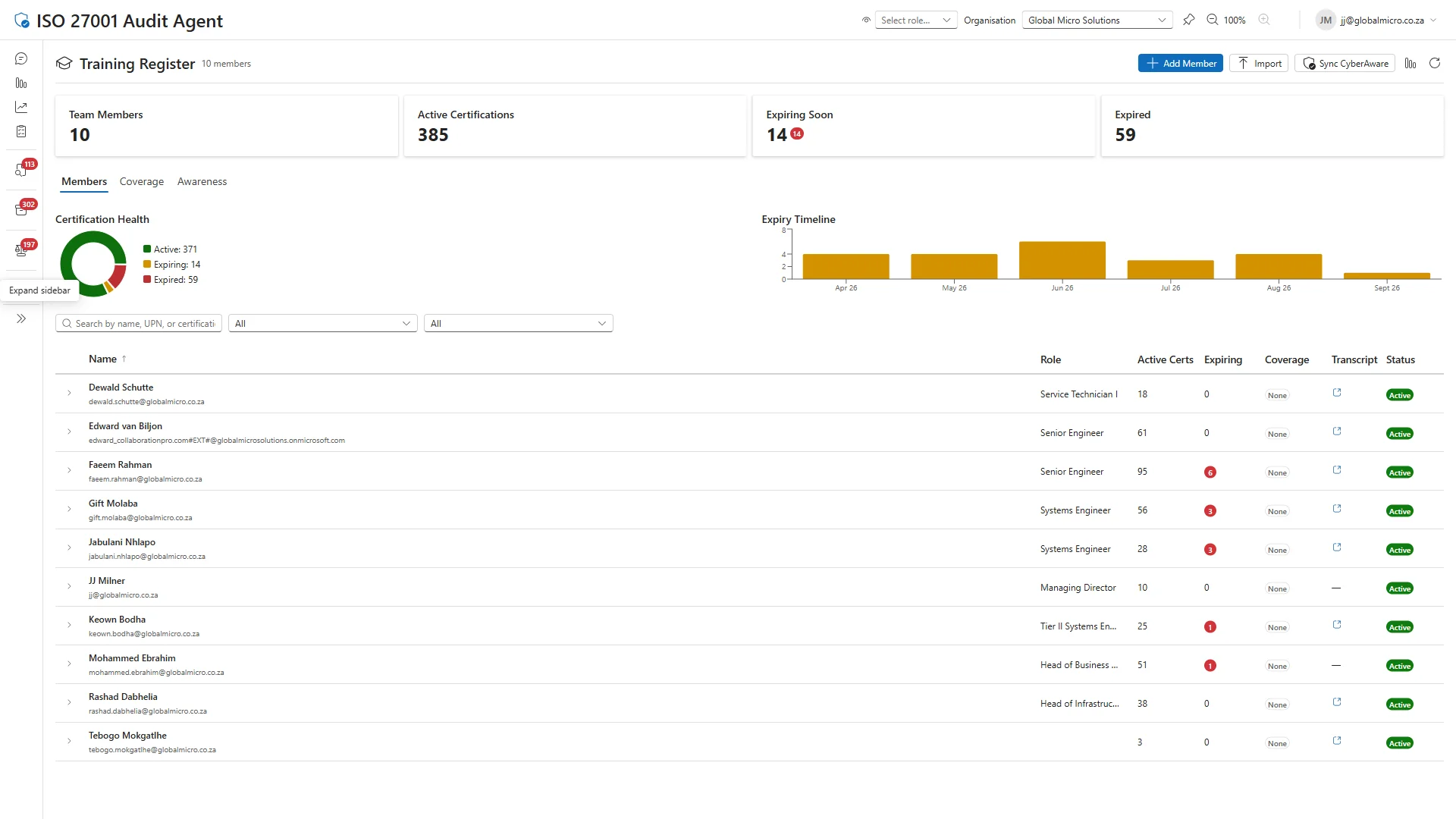
- Awareness Register & Compliance Evidence — Automated awareness tracking in the Audit Agent — per-learner completion (due, completed, overdue, failed), risk scoring with trend analysis (improving/worsening/stable), engagement flags (never engaged, low, good), campaign history, and overdue alerts. Cross-references CyberAware data via UPN matching. Feeds directly into ISO 27001 A.6.3 evidence — when the auditor asks, the register is already there.
- Training Register & Capability Mapping — Tracks professional development across the team in the Audit Agent — Microsoft certifications (AZ-500, SC-300, MS-700), vendor qualifications, and capability coverage mapping for workloads including Exchange, Intune, Sentinel, and Purview. Monitors training plans with target completion dates and flags single-point-of-failure risks where only one individual holds certification for a capability. Feeds into ISO 27001 A.6.3 and A.6.6 evidence alongside the awareness data.
What you receive
| Delivery Package | Duration | Stakeholders | Key Deliverables |
|---|---|---|---|
| Security Awareness & Human Risk | 3–10 days | CISO, IT Admin, HR, Compliance Officer | CyberAware platform configured with initial training campaigns; Attack Simulation Training campaigns deployed via Defender for O365 P2; Awareness Register configured in Audit Agent with learner sync; A.6.3 evidence automation activated; Awareness policy document referencing actual platform configuration |
We deploy the CyberAware platform and Attack Simulation Training, then operate continuous campaigns — dynamic enrolment, remedial training, and targeted phishing simulations that adapt as your organisation matures. Then we prove it: the Awareness Register delivers automated, auditor-ready evidence of completion rates, risk scores, engagement metrics, and training plans. When the auditor asks for your A.6.3 evidence, it is already there.
Risk impact
| Risk | Before | After | Reduction |
|---|---|---|---|
| Policy Non-Compliance by Staff | 16 | 3 | 81% |
| Poor Staff Offboarding | 12 | 2 | 83% |
Risk scores use a likelihood × impact matrix (1–25). Lower is better.
Ready to see where you stand? Our free assessment benchmarks your security awareness & human risk against these capabilities — in 30 minutes, no tenant access required. Start your assessment.
ISO 27001 controls covered
- A.5.10 Acceptable Use of Information and Other Associated Assets
- A.5.4 Management Responsibilities
- A.6.1 Screening
- A.6.2 Terms and Conditions of Employment
- A.6.3 Information Security Awareness, Education and Training
- A.6.6 Confidentiality or Non-Disclosure Agreements