Data Protection & Governance
Data Loss Prevention, sensitivity labels, information protection, and retention policies.
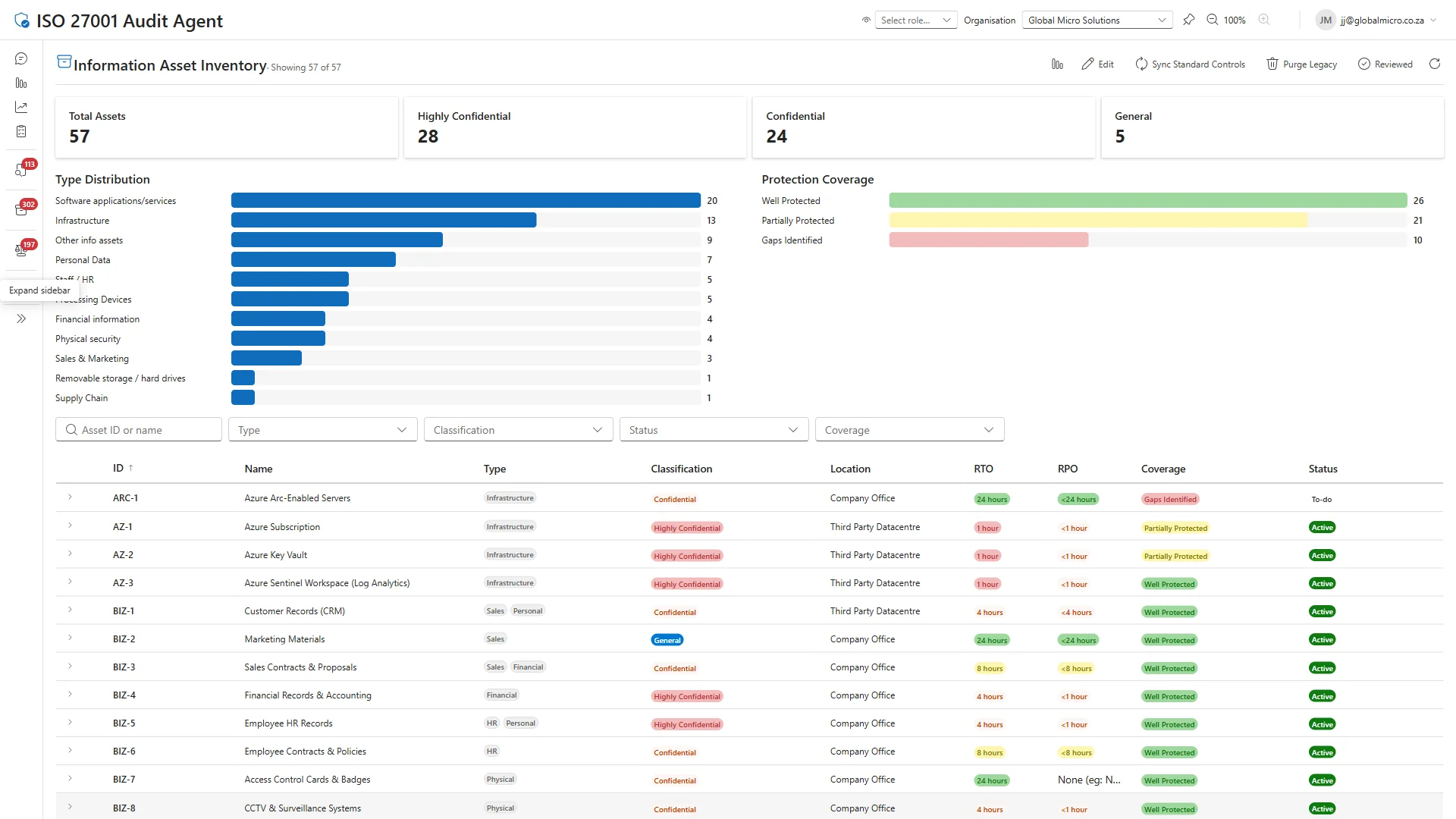
Your data classified, labelled, and protected before the auditor asks.
Data sprawl is the silent compliance killer. Your sensitive information flows through email, Teams, and SharePoint with little visibility or control — and every unclassified document is a finding waiting to happen. We deploy sensitivity labels, DLP policies, and retention rules that transform data governance from aspiration to auditable proof.
Here is the complete data protection stack we deploy. Every label, every policy, every rule produces classification and protection evidence.
Added in Information Governance (Plan 3)
- Sensitivity Label Taxonomy — Define and publish sensitivity label taxonomy with stakeholders
- Manual Labeling — Deploy manual sensitivity labeling to users
- Label-Based Encryption — Configure sensitivity labels with encryption protection
- Client-Side Auto-Labeling — Configure automatic labeling recommendations in Office clients
- Service-Side Auto-Labeling — Configure automatic labeling policies for SharePoint, OneDrive, Exchange
- Exchange DLP — Data Loss Prevention policies for Exchange Online
- SharePoint/OneDrive DLP — Data Loss Prevention policies for SharePoint and OneDrive
- Teams DLP — Data Loss Prevention policies for Microsoft Teams
- Custom Sensitive Information Types — Create custom SITs for organisation-specific data patterns
- Endpoint DLP — Data Loss Prevention for Windows endpoints
- Exact Data Match — EDM-based sensitive information types for precise data matching
- Trainable Classifiers — Machine learning classifiers for content classification
- Joiner Entitlement Packages — Identity Governance lifecycle workflows for new starters
- Leaver Entitlement Packages — Identity Governance lifecycle workflows for leavers
- Access Reviews - Basic — Quarterly access reviews for privileged roles and groups
- Access Reviews - Full — Comprehensive access reviews including application access
What you receive
| Delivery Package | Duration | Stakeholders | Key Deliverables |
|---|---|---|---|
| Information Protection | 10–25 days | CISO, Data Owners, Legal, End Users | Label taxonomy document; Label publishing policy; Encryption configuration; Auto-labelling rules; User training materials |
| Data Loss Prevention | 10–25 days | CISO, Compliance, Legal | DLP policy matrix; Custom SIT definitions (SA identifiers); Endpoint DLP configuration; EDM schema and data source; Policy testing and tuning report |
| Identity Governance & Lifecycle | 8–20 days | HR, IT Admin, Line Managers | Role-to-access package mapping; Lifecycle workflow definitions; HR connector configuration; Joiner/mover/leaver automation |
Risk impact
| Risk | Before | After | Reduction |
|---|---|---|---|
| Personal Data Privacy Breach | 20 | 4 | 80% |
| Insecure Data Sharing | 16 | 3 | 81% |
| Classification and Versioning Failures | 12 | 2 | 83% |
| Intellectual Property Mismanagement | 12 | 2 | 83% |
| Portable Storage Data Loss | 12 | 2 | 83% |
Risk scores use a likelihood × impact matrix (1–25). Lower is better.
Ready to see where you stand? Our free assessment benchmarks your data protection & governance against these capabilities — in 30 minutes, no tenant access required. Start your assessment.
ISO 27001 controls covered
- A.5.12 Classification of Information
- A.5.13 Labelling of Information
- A.5.16 Identity Management
- A.5.18 Access Rights
- A.6.1 Screening
- A.6.5 Responsibilities After Termination or Change of Employment
- A.8.12 Data Leakage Prevention
- A.8.24 Use of Cryptography